Secured and Unsecured Config
Secured and Unsecured Config is used to keep the configuration data that is used inside the plugin code and we don’t want to have those as the hardcode in the code. And when there is a lot of custom extension required in a Dynamics CRM project. We require having an ample amount of plugins register for functionality extension and at the same time. It becomes difficult to keep the configuration data in the code repository as it would need to have multiple Config files maintained. On the other hand, if we don’t keep Config inside the code repository, there might be chances of losing those on the application crash.
While working, if Dynamics CRM Consultants use an insecure/secure Config, we may place a JSON file inside the plugin project to avoid hardcodes in our plugin code. For better code creation instead of using an insecure/secure Config.

However, a separate file cannot register on the Dynamics CRM server, so we need to go through the following steps to embed the file in the assembly itself.
Steps:
1. Put all the configurations into JSON format and segregate those into that JSON file either categorizing by entity name or event or both. For example, suppose we have an unsecured configuration with the plugin step registered on the account entity. Also the configuration of the opportunity entity. In that case, we can define our JSON as follows.
2. Add the JSON file into the plugin project and go to the properties of the included file to set the Build Action as “Embedded Resource”.

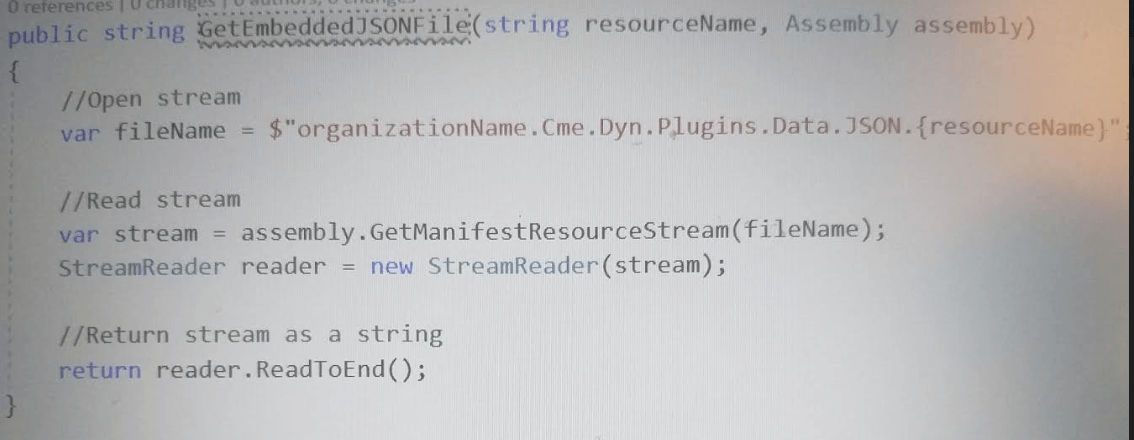
3. The following function is used to read the file. The file name in the below code should be replaced with the Plugin assembly name.<folder in which file is kept inside>.<Resource Name or JSON file name>
In the below example, “OrganizationName.Cme.Dyn.Plugins” is the assembly name. “Data” is the first folder and “JSON” is the folder into “Data”, and the JSON file is kept there itself.
4. Retuned Byte stream from the above-mentioned function converted into JSON format using JSON serialize to get the values from the configurations.
Conclusion
Rather than using Unsecured/Secured configurations, we can have JSON files embedded with assembly to keep all the hardcode values, which easily maintained in the code repository.



